Download our cybersecurity risk assessment guide
Learn how to safeguard your business against cyberattacks and protect your data with our comprehensive guide
How it Works
These functions are designed to provide a high-level, strategic view of an organization's management of cybersecurity risk, helping organizations achieve a secure, compliant, and resilient cybersecurity posture.

Does everyone know their role in your organization?

How do you identify your network assets?

How do you protect your network?

How do you detect threats on your network?

How do you respond to threats to your network?

How do you recover from threats on your network?

The QMI Advantage: Hacking Defense Excellence
The Quantify, Measure, and Improve (QMI) framework is our secret sauce for superior defense. Built on years of experience across the entire security lifecycle (Govern, Identify, Protect, Detect, Respond, Recover), QMI ensures measurable security maturity and safeguards organizations like yours from sophisticated threats.
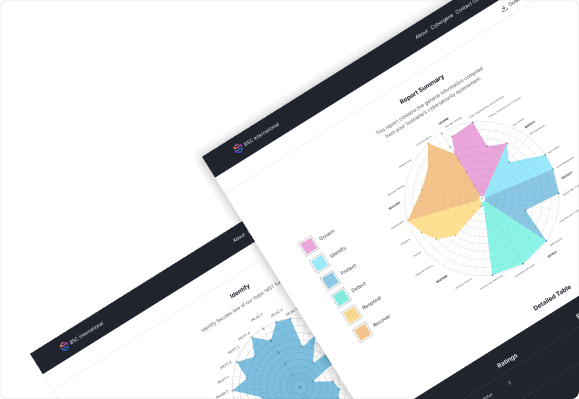
Get a more comprehensive report when you sign up for audit
With audit, we provide your organization with a detailed report, with a simplified breakdown using charts and table. You will also have access to a personlized dashboard for full control and future reference
- Basic Report
- Basic graphic report
- Freeware dashboard
- Report History
- Dashboard
- Detailed Report
- Report History
- Free One Hours Consultation with our CIO
Let's Meet Our Cybersecurity Experts
Stop Doubting. Start Achieving. Talk to Our Experts.
